Open-source software tools and Vault maker HashiCorp has disclosed a security incident that occurred due to the recent Codecov attack.
HashiCorp, a Codecov customer, has stated that the recent Codecov supply-chain attack aimed at collecting developer credentials led to the exposure of HashiCorp’s GPG signing key.
The private key is used by HashiCorp to sign and verify software releases, and has since been rotated as a precaution.
HashiCorp discloses code-signing key compromise
This week, HashiCorp, a notable open-source software tools and infrastructure provider, disclosed that the recent Codecov supply-chain attack had impacted a subset of their Continuous Integration (CI) pipelines.
The company states that as a result of this, the GPG key used by HashiCorp to sign and verify software releases was exposed.
Codecov provides software testing and code coverage services to over 29,000 customers.
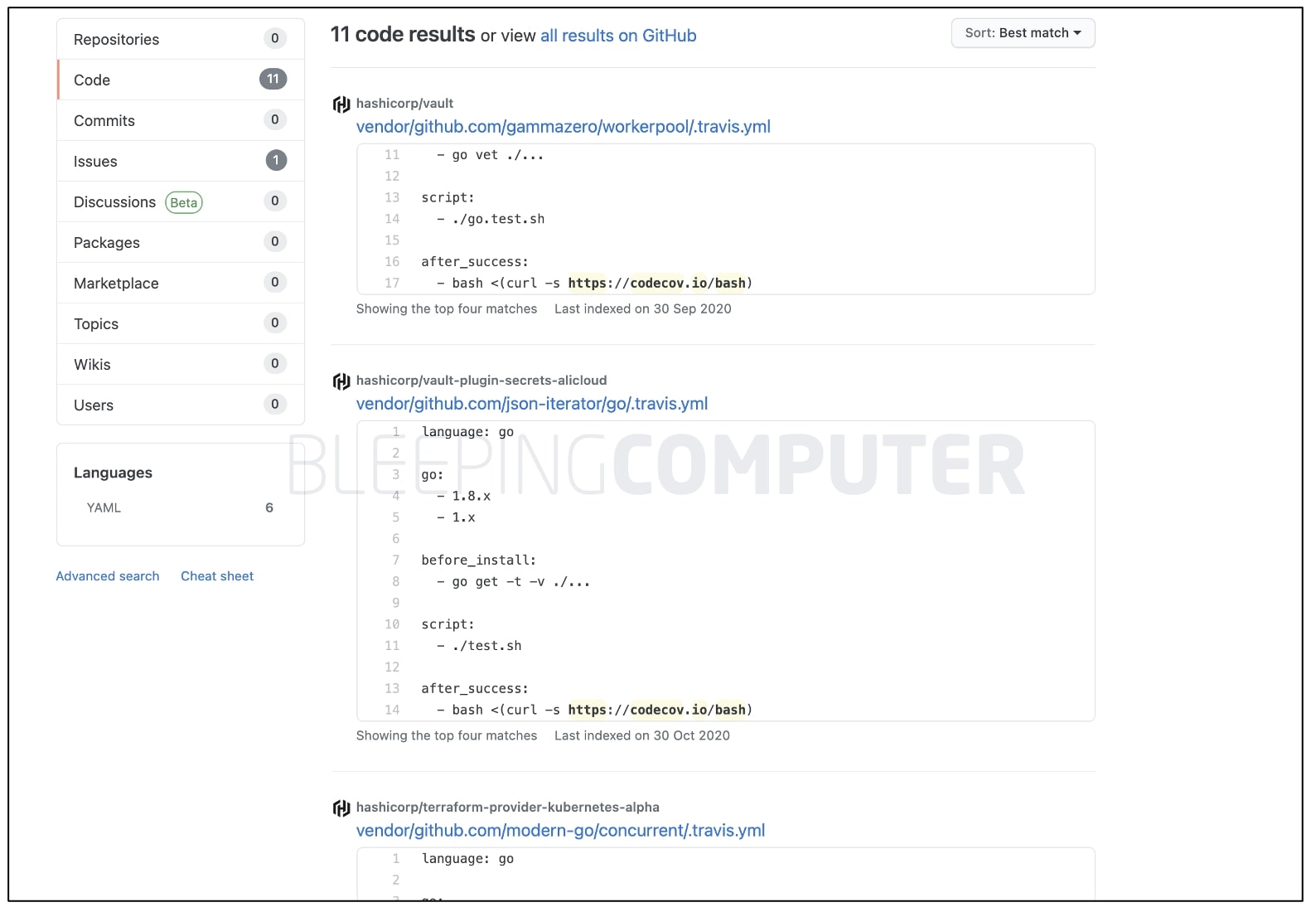
On April 1st, Codecov had learned that due to a flaw in their Docker image, threat actors had obtained credentials to the Bash Uploader scripts used by their customers.
The Bash Uploaders were modified with a malicious line of code that exfiltrated environment variables and secrets collected from some customers’ CI/CD environments, to an attacker-controlled server.
According to Codecov’s investigation, the initial compromise of the Bash Uploader happened on January 31, making this attack last around two months.
In all this, HashiCorp’s GPG private keythat signs hashes used to verify HashiCorp’s product downloads was exposed.
“While investigation has not revealed evidence of unauthorized usage of the exposed GPG key, it has been rotated in order to maintain a trusted signing mechanism.”
A new GPG keypair (fingerprint shown below) has been published that is to be used from now on:C874 011F 0AB4 0511 0D02 1055 3436 5D94 72D7 468F
The older, compromised GPG keypair (fingerprint shown below) has been revoked:91A6 E7F8 5D05 C656 30BE F189 5185 2D87 348F FC4C
“Existing releases have been validated and re-signed,” states HashiCorp in a security event disclosure.
According to HashiCorp, this incident has only impacted HashiCorp’s SHA256SUM signing mechanism.
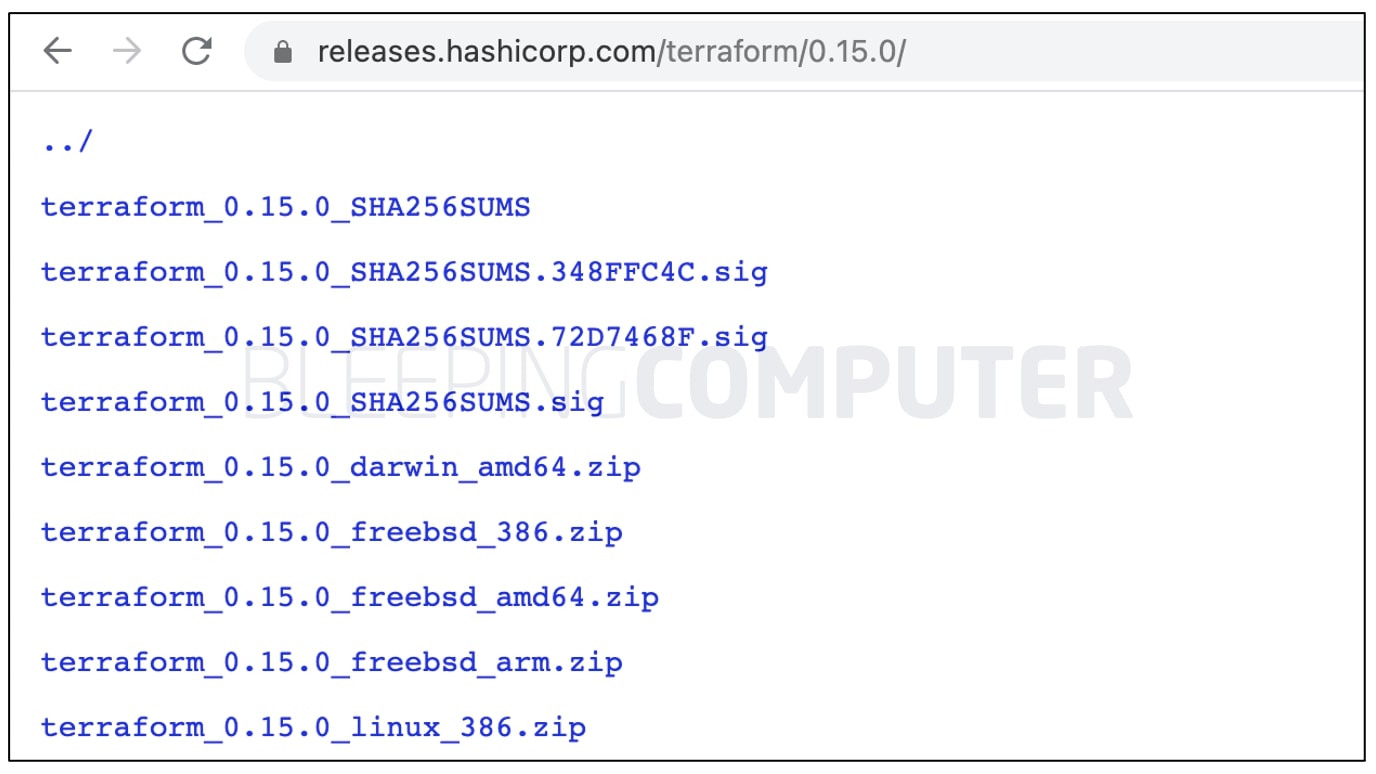
MacOS code signing (notarization), as well as, Windows AuthentiCode signing of HashiCorp releases, has not been affected by the exposed private key.
Likewise, signing for Linux packages (Debian and RPM) available on releases.hashicorp.com remains unaffected.
HashiCorp’s Terraform yet to be patched
However, HashiCorp’s advisory does state that their Terraform product is yet to be patched to use the new GPG key.
Terraform is an open-source infrastructure-as-code software tool used for safely and predictably creating, changing, and improving infrastructure.
“Terraform automatically downloads provider binaries during the terraform init operation and performs signature verification during this process,” states Jamie Finnigan, HashiCorp’s Director of Product security.
The company states that patched releases of Terraform and related tools will be published that use the new GPG key during automatic code verification.
“In the short term, transport-level TLS protects official Terraform provider binaries downloaded during init, and manual verification of Terraform and its providers can be performed with the new key and signatures as described at https://hashicorp.com/security,” continues Finnigan in the security advisory.
As a part of its incident response activities, HashiCorp is further investigating if any other information was exposed from the Codecov incident and plans on providing relevant updates, as the investigation progresses.
As reported by BleepingComputer earlier this week, hundreds of Codecov customer networks were reportedly breached due to the Codecov Bash Uploader compromise.
U.S. federal investigators have also stepped in and are working with Codecov and their customers, to investigate the full impact of the attack.
As such, more security disclosures are expected to come out in the following weeks from different customers.
Software supply-chain attacks continue to be on the rise as they become the latest focus of threat actors.
Just yesterday, BleepingComputer reported that the Passwordstate enterprise password manager used by many Fortune 500 customers was hacked in a supply-chain attack.



























You must be logged in to post a comment Login